Postfixの設定
外部からWebアクセスできるようにします。
root@www:~# vi /etc/apache2/sites-available/virtualhost-00-ubuntuserver.jp.conf
<VirtualHost *:80>
ServerName ubuntuserver.jp
DocumentRoot /var/www/html
ServerAlias mail.ubuntuserver.jp
RewriteEngine On
RewriteCond %{HTTP_HOST} ^ubuntuserver\.jp
RewriteRule ^(.*)$ http://ubuntuserver.jp/$1 [R=301,L]
</VirtualHost>
Postfixをインストールします。
root@www:~# apt-get -y install postfix
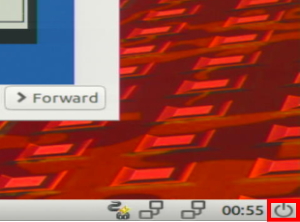
← →キーで「了解」を選択して「Enter」キーを押下します。
↑ ↓ キーで「設定なし」を選択し、← →キーで「了解」を選択して「Enter」キーを押下します。
Postfixを設定します。
root@www:~# cp /usr/share/postfix/main.cf.dist /etc/postfix/main.cf
root@www:~# vi /etc/postfix/main.cf
78行目:行頭の「#」を削除してコメント解除します。
mail_owner = postfix
94行目:行頭の「#」を削除してコメント解除し、メールサーバードメイン名を指定します。
myhostname = mail.ubuntuserver.jp
102行目:行頭の「#」を削除してコメント解除し、ドメイン名を指定します。
mydomain = ubuntuserver.jp
123日行目:行頭の「#」を削除してコメント解除し、送信元メールアドレスにドメイン名を指定します。
myorigin = $mydomain
137行目:行頭の「#」を削除してコメント解除します。
inet_interfaces = all
185行目:行頭の「#」を削除してコメント解除し、ドメインメールを受信する設定に変更します。
mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain
228行目:行頭の「#」を削除してコメント解除します。
local_recipient_maps = unix:passwd.byname $alias_maps
270行目:行頭の「#」を削除してコメント解除します。
mynetworks_style = subnet
287行目:ネットワーク設定を追記します。
mynetworks = 127.0.0.0/8, 192.168.1.1/24
407行目:行頭の「#」を削除してコメント解除します。
alias_maps = hash:/etc/aliases
418行目:行頭の「#」を削除してコメント解除します。
alias_database = hash:/etc/aliases
440行目:行頭の「#」を削除してコメント解除し、メール格納形式をMaildir形式にする設定をします。
home_mailbox = Maildir/
576行目:行頭に「#」を追記してコメント化します。
#smtpd_banner = $myhostname ESMTP $mail_name (Ubuntu)
577行目:メールサーバーソフト名の隠蔽化の設定を追記します。
smtpd_banner = $myhostname ESMTP unknown
650行目:sendmailパスの設定を追記します。
sendmail_path = /usr/sbin/postfix
655行目:メールの転送の設定を追記します。
newaliases_path = /usr/bin/newaliases
660行目:メールキューの設定を追記します。
mailq_path = /usr/bin/mailq
666行目:送信メッセージの一時格納場所のグループの設定を追記します。
setgid_group = postdrop
670行目:行頭に「#」を追記してコメント化します。
#html_directory =
674行目:行頭に「#」を追記してコメント化します。
#manpage_directory =
679行目:行頭に「#」を追記してコメント化します。
#sample_directory =
683行目:行頭に「#」を追記してコメント化します。
#readme_directory =
SMTP認証の設定を最終行へ追加します。
smtpd_sasl_type = dovecot
smtpd_sasl_path = private/auth
smtpd_sasl_auth_enable = yes
smtpd_sasl_security_options = noanonymous
smtpd_sasl_local_domain = $myhostname
smtpd_recipient_restrictions = permit_mynetworks, permit_auth_destination, permit_sasl_authenticated, reject
受信メールサイズを10MB=10*1024*1024に制限する設定を最終行へ追記します。
message_size_limit = 10485760
master.cfを設定します。
root@www:~# vi /etc/postfix/master.cf
17行目:行頭の「#」を削除してコメント解除します。
submission inet n - n - - smtpd
20行目:行頭の「#」を削除してコメント解除します。
-o smtpd_sasl_auth_enable=yes
設定を有効にします。
root@www:~# newaliases
再起動します。
root@www:~# systemctl restart postfix
Dovecotのインストール
root@www:~# apt-get -y install dovecot-core dovecot-pop3d dovecot-imapd
dovecot.confを設定します。
root@www:~# vi /etc/dovecot/dovecot.conf
30行目:行頭「#」を削除してコメント解除し、IPv6を無効にする設定に変更します。
listen = *
10-mail.confを設定します。
root@www:~# vi /etc/dovecot/conf.d/10-mail.conf
31行目:メール格納形式をMaildir形式にする設定に変更します。
mail_location = maildir:~/Maildir
10-auth.confを設定します。
root@www:~# vi /etc/dovecot/conf.d/10-auth.conf
10行目:行頭「#」を削除してコメント解除し、プレインテキスト認証を許可する設定を追記します。
disable_plaintext_auth = no
10-ssl.confを設定します。
root@www:~# vi /etc/dovecot/conf.d/10-ssl.conf
6行目:SSL接続を無効にする設定に変更します。
ssl = no
起動します。
root@www:~# systemctl restart dovecot
SMTP認証設定
cyrus-saslをインストールします。
root@www:~# apt-get -y install sasl2-bin cyrus-sasl-plain
起動します。
root@www:~# systemctl start saslauthd
Maildir形式メールボックスの作成
新規ユーザー追加時に自動でMaildir形式メールボックス作成する設定をします。
root@www:~# mkdir -p /etc/skel/Maildir/{new,cur,tmp}
メールボックスパーミッションを設定します。
root@www:~# chmod -R 700 /etc/skel/Maildir/
起動します。
root@www:~# systemctl restart postfix
現在のユーザーのMaildir形式メールボックス作成する設定をします。
[root@www ~]# wget https://rcg.jp/perfect_maildir/perfect_maildir.pl -O /usr/local/bin/perfect_maildir.pl
[root@www ~]# chmod +x /usr/local/bin/perfect_maildir.pl
Maildir変換に必要なPerlのTimeDateモジュールインストールします。
[root@www ~]# apt-get -y install perl-TimeDate
Postfixを停止します。
[root@www ~]# systemctl stop postfix
Maildir一括変換スクリプトを作成します。
[root@www ~]# vi migrate-maildir.sh
#!/bin/bash
#
#Maildir一括変換スクリプト
#
#メールボックス=>Maildir形式変換スクリプト
#http://perfectmaildir.home-dn.net/
FOLDERCONVERT=/usr/local/bin/perfect_maildir.pl
#一般ユーザリスト
USERLIST=`ls /home/`
#ログ
MIGRATELOG=/tmp/migrate-maildir.log
rm -f $MIGRATELOG
#引数(変換元メールボックス形式)チェック
if [ "$1" != "mbox" ] && [ "$1" != "Mailbox" ]; then
echo "Usage: migrate-maildir.sh {mbox|Mailbox}"
exit
fi
#一般ユーザメールボックス移行
for user in $USERLIST;
do
if [ "$1" = "mbox" ]; then
inbox="/var/spool/mail/${user}"
else
inbox="/home/${user}/Mailbox"
fi
if [ -f "${inbox}" ]; then
newdir="/home/${user}/Maildir/"
mkdir -p "$newdir"
mkdir -p "$newdir"/cur
mkdir -p "$newdir"/new
mkdir -p "$newdir"/tmp
chmod -R 700 "${newdir}"
$FOLDERCONVERT "$newdir" < "${inbox}" >> $MIGRATELOG 2>&1
chown -R ${user}. "$newdir"
find "$newdir" -type f -exec chmod 600 {} \;
fi
done
#rootユーザメールボックス移行
user="root"
if [ "$1" = "mbox" ]; then
inbox="/var/spool/mail/${user}"
else
inbox="/${user}/Mailbox"
fi
if [ -f "${inbox}" ]; then
newdir="/${user}/Maildir/"
mkdir -p "$newdir"
mkdir -p "$newdir"/cur
mkdir -p "$newdir"/new
mkdir -p "$newdir"/tmp
chmod -R 700 "${newdir}"
$FOLDERCONVERT "$newdir" < "${inbox}" >> $MIGRATELOG 2>&1
chown -R ${user}. "$newdir"
find "$newdir" -type f -exec chmod 600 {} \;
fi
[ -a $MIGRATELOG ] && cat $MIGRATELOG;rm -f $MIGRATELOG
一括変換スクリプトを実行します。
[root@www ~]# sh migrate-maildir.sh mbox
Maildir一括変換スクリプトを削除します。
[root@www ~]# rm -f migrate-maildir.sh
Maildir変換ツールを削除します。
[root@www ~]# rm -f /usr/local/bin/perfect_maildir.pl
起動します。
[root@www ~]# systemctl restart postfix dovecot
webmasterユーザーをメール使用する場合は「/etc/aliases」を変更します。
[root@www ~]# vi /etc/aliases
行頭に#を追加して転送を無効にします。
#webmaster: root
転送設定を反映します。
[root@www ~]# newaliases
TCP25番、TCP587番ポート開放
ルーターの設定で、TCP25番、TCP587番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
ポート開放テスト
こちらのサイトで「ホスト名(ubuntuserver.jp)」、「ポート番号(25,587)」の開放確認をします。
メールサーバーのOP25B対策
メールサーバーのOP25B対策として送信メールをGmailを経由して送信するように設定します。
Postfixを設定します。
root@www:~# vi /etc/postfix/main.cf
以下を最終行へ追加します。
relayhost = [smtp.gmail.com]:587
smtp_use_tls = yes
smtp_sasl_auth_enable = yes
smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd
smtp_sasl_tls_security_options = noanonymous
smtp_sasl_mechanism_filter = plain
SMTP認証情報を設定します。
root@www:~# echo [smtp.gmail.com]:587 Gmailアドレス:Gmailパスワード > /etc/postfix/sasl_passwd
root以外参照できないようにパーミッション変更します。
root@www:~# chmod 640 /etc/postfix/sasl_passwd
SMTP認証情報をデータベース化します。
root@www:~# postmap /etc/postfix/sasl_passwd
Postfixを再起動します。
root@www:~# systemctl reload postfix
Gmailのメール転送設定
先にThunderbirdへGmail(送信用メール)を設定します。
Thunderbirdを起動し、送信用メールアドレスで「ブロックされたログインについてご確認ください」を開き、「安全性の低いアプリへのアクセスを許可」をクリックします。
ブラウザでGmailにログインします。
右上のユーザーアイコンを右クリック→「Googleアカウントの管理」→「セキュリティ」→「安全性の低いアプリのアクセス」でアクセスを有効にします。
TCP110番またはTCP143番ポート開放
ルーターの設定で、TCP110番またはTCP143番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
ポート開放テスト
こちらのサイトで「ホスト名(ubuntuserver.jp)」、「ポート番号(110または143)」の開放確認をします。
メールユーザーの追加
ユーザーを追加します。(ユーザー例:ubuntu)
root@www:~# useradd ubuntu
パスワードを設定します。
root@www:~# passwd ubuntu
Changing password for user ubuntu.
New UNIX password:
Retype new UNIX password:
「/etc/ssh/sshd_config」を編集して、秘密鍵での認証接続を無効にする
sshd_configを編集します。
root@www:~# vi /etc/ssh/sshd_config
52行目:「no」→「yes」に変更します。
PasswordAuthentication yes
SSHを再起動します。
root@www:~# systemctl restart sshd
TeraTermにubuntuで新しい接続をします。
SSHサーバー公開鍵認証方式接続の設定をします。
メールソフトの登録
Thunderbirdを起動し、メールをクリックします。
あなたのお名前、メールアドレス(ubuntu@ubuntuserver.jp)、パスワードを入力し、「続ける」をクリックします。
「手動設定」をクリックします。
|
|
サーバーのホスト名 |
ポート番号 |
SSL |
認証方式 |
| 受信サーバー |
POP3 |
mail.ubuntuserver.jp |
110 |
接続の保護なし |
通常のパスワード認証 |
| 送信サーバー |
SMTP |
mail.ubuntuserver.jp |
587 |
接続の保護なし |
通常のパスワード認証 |
上の表を参考にして設定し、「完了」をクリックします。
「接続する上での危険性を理解しました」を選択して「完了」をクリックします。
サーバー証明書の取得
Certbotをインストールします。
root@www:~# apt -y install certbot
証明書を取得します。
ドキュメントルート:/var/www/html/
メールアドレス:webmaster@ubuntuerver.jp
メールサーバー名:mail.ubuntuserver.jp
root@www:~# certbot certonly --webroot -w /var/www/html/ -m webmaster@ubuntuserver.jp -d mail.ubuntuserver.jp --agree-tos
証明書自動更新を設定します。
root@www:~# vi /etc/cron.d/letsencrypt
下記を追記します。
00 16 * * 2 root /usrobin/certbot renew --post-hook "service httpd restart"
SSLの設定
main.cfを設定します。
root@www:~# vi /etc/postfix/main.cf
下記を最終行に追記します。
smtp_tls_security_level = may
smtpd_tls_security_level = may
smtpd_tls_cert_file = /etc/letsencrypt/live/mail.ubuntuserver.jp/fullchain.pem
smtpd_tls_key_file = /etc/letsencrypt/live/mail.ubuntuserver.jp/privkey.pem
smtpd_tls_session_cache_database = btree:/var/lib/postfix/smtpd_scache
tls_high_cipherlist = kEECDH:+kEECDH+SHA:kEDH:+kEDH+SHA:+kEDH+CAMELLIA:kECDH:+kECDH+SHA:kRSA:+kRSA+SHA:+kRSA+CAMELLIA:!aNULL:!eNULL:!SSLv2:!RC4:!MD5:!DES:!EXP:!SEED:!IDEA:!3DES
smtp_tls_ciphers = high
smtpd_tls_ciphers = high
smtpd_tls_mandatory_ciphers = high
smtpd_tls_mandatory_protocols=!SSLv2,!SSLv3
smtp_tls_mandatory_protocols=!SSLv2,!SSLv3
smtpd_tls_protocols=!SSLv2,!SSLv3
smtp_tls_protocols=!SSLv2,!SSLv3
master.cfを設定します。
root@www:~# vi /etc/postfix/master.cf
17行目:行頭に「#」を追加してコメント化し、SUBMISSIONポートを無効化します。
#submission inet n - n - - smtpd
20行目:行頭に「#」を追加してコメント化し、SUBMISSIONポートのSMTP認証を無効化します。
# -o smtpd_sasl_auth_enable=yes
28行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
smtps inet n - n - - smtpd
30行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
-o smtpd_tls_wrappermode=yes
31行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
-o smtpd_sasl_auth_enable=yes
44行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
tlsmgr unix - - n 300 1 tlsmgr
再起動します。
root@www:~# systemctl restart postfix
TCP465番ポート開放
ルーターの設定で、TCP465番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
ポート開放テスト
こちらのサイトで「ホスト名(mail.ubuntuserver.jp)」、「ポート番号(465)」の開放確認をします。
TCP587番ポート閉鎖
ルーターの設定で、TCP587番ポートを閉鎖します。(設定方法はご自身の環境に合わせて調べてください。)
ポート開放テスト
こちらのサイトで「ホスト名(mail.ubuntuserver.jp)」、「ポート番号(587)」の開放されていないことを確認をします。
Dovecot設定
10-auth.confを設定します。
root@www:~# vi /etc/dovecot/conf.d/10-ssl.conf
6行目:SSL接続を有効にする設定に変更します。
ssl = yes
12行目:行頭の「#」を削除してコメント解除し、サーバー証明書+中間証明書を指定します。
ssl_cert = </etc/letsencrypt/live/mail.ubuntuserver.jp/fullchain.pem
13行目:行頭の「#」を削除してコメント解除し、秘密鍵を指定します。
ssl_key = </etc/letsencrypt/live/mail.ubuntuserver.jp/privkey.pem
49行目:行頭の「#」を削除してコメント解除し、脆弱性のある暗号化方式(SSLv2,SSLv3)を無効化します。
ssl_protocols = !SSLv2 !SSLv3
52行目:行頭の「#」を削除してコメント解除し、使用する暗号化方法を指定します。
ssl_cipher_list = EECDH+AESGCM+AES128:EECDH+AESGCM+AES256:EDH+AESGCM+AES128:EDH+AESGCM+AES256:EECDH+SHA256+AES128:EECDH+SHA384+AES256:EDH+SHA256+AES128:EDH+SHA256+AES256:EECDH+SHA1+AES128:EECDH+SHA1+AES256:EDH+SHA1+AES128:EDH+SHA1+AES256:EECDH+HIGH:EDH+HIGH:AESGCM+AES128:AESGCM+AES256:SHA256+AES128:SHA256+AES256:SHA1+AES128:SHA1+AES256:HIGH:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!KRB5:!aECDH:!3DES
再起動します。
root@www:~# systemctl restart dovecot
TCP995番またはTCP993番ポート開放
ルーターの設定で、TCP995番またはTCP993番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
ポート開放テスト
こちらのサイトで「ホスト名(mail.ubuntuserver.jp)」、「ポート番号(995または993)」の開放確認をします。
メールソフトの設定変更
Thunderbirdを起動し、メールアドレスを選択し、「このアカウントの設定を表示する」をクリックします。
「サーバー設定」をクリックし、「接続の保護」で「SSL/TLS」を選択します。
「送信(SMTP)サーバー」をクリックし、SMTPサーバーを選択して「編集」をクリックします。
「ポート番号」に「465」を入力し、「接続の保護」で「SSL/TLS」を選択して、「OK」をクリックします。
「OK」をクリックします。
アンチウィルスソフトの連携(Clamav)
Clamav をインストールします。
root@www:~# apt-get -y install clamav-daemon clamsmtp
clamsmtpd.confを設定します。
root@www:~# vi /etc/clamsmtpd.conf
27行目:行頭の「#」を削除してコメント解除します。
Header: X-AV-Checked: ClamAV using ClamSMTP
45行目:変更します。
User: clamav
設定を有効にします。
root@www:~# chown -R clamav. /var/spool/clamsmtp
root@www:~# chown -R clamav. /var/run/clamsmtp
main.cfを設定します。
root@www:~# vi /etc/postfix/main.cf
最終行へ追記します。
content_filter = scan:127.0.0.1:10026
master.cfを設定します。
root@www:~# vi /etc/postfix/master.cf
最終行へ追記します。
scan unix - - n - 16 smtp
-o smtp_data_done_timeout=1200
-o smtp_send_xforward_command=yes
-o disable_dns_lookups=yes
127.0.0.1:10025 inet n - n - 16 smtpd
-o content_filter=
-o local_recipient_maps=
-o relay_recipient_maps=
-o smtpd_restriction_classes=
-o smtpd_client_restrictions=
-o smtpd_helo_restrictions=
-o smtpd_sender_restrictions=
-o smtpd_recipient_restrictions=permit_mynetworks,reject
-o mynetworks_style=host
-o smtpd_authorized_xforward_hosts=127.0.0.0/8
再起動します。
root@www:~# systemctl restart clamav-daemon clamsmtp postfix