起動不能をインストールDVDで復旧
起動不能をインストールDVDで復旧します。
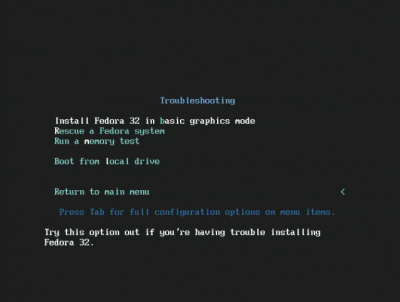
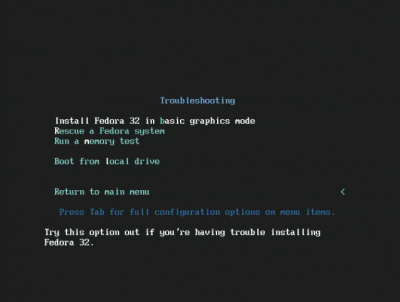
インストールDVDを投入して起動後、「Troubleshooting」を選択し「Enter」キーを押下します。

「Rescue a Fedora system」を選択し「Enter」キーを押下します。
「1」(continue)を入力し「Enter」キーを押下します。
「Enter」キーを押下します。
インストールDVDを取り出して、「reboot」と入力して、「Enter」キーを押下します。
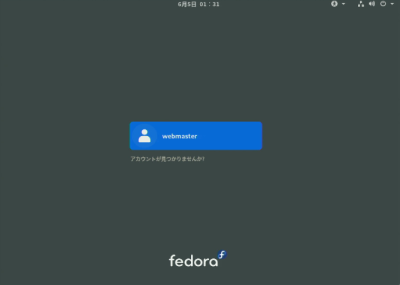
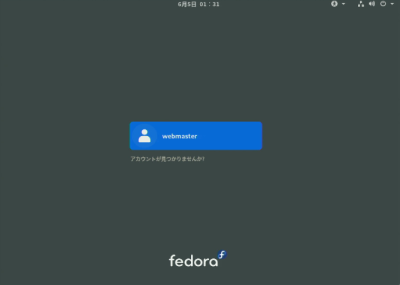
起動を確認します。
Linuxサーバー、WordPress、Androidの情報やゲーム、DIYなど色々な情報をご紹介致します。
自宅サーバー、自宅ファイルサーバー、Linuxサーバー構築の初心者におすすめ!コピペ(コピー&ペースト)でできる自宅サーバーFedora・Ubuntu・Debian・Linux Mint・AlmaLinux・CentOS(Linux)の作り方。初心者の方でもコピー、貼付けでLinux自宅サーバーを簡単に作れるように説明しています。Webサーバー、メールサーバー、VPNサーバー、WordPressなどを設定します。
起動不能をインストールDVDで復旧します。
インストールDVDを投入して起動後、「Troubleshooting」を選択し「Enter」キーを押下します。

「Rescue a Fedora system」を選択し「Enter」キーを押下します。
「1」(continue)を入力し「Enter」キーを押下します。
「Enter」キーを押下します。
インストールDVDを取り出して、「reboot」と入力して、「Enter」キーを押下します。
起動を確認します。
s50
複数ドメイン用ディレクトリを作成します。
[root@www ~]# 50_1mkdir /var/www/html/virtual.jp
s51パーミッションを設定します。
[root@www ~]# 51_1chmod 777 /var/www/html/virtual.jp
s52複数ドメイン用設定ファイルを作成します。
[root@www ~]# 52_1vi /etc/httpd/conf.d/virtualhost-virtual.jp.conf 53_1<VirtualHost *:80> ServerName virtual.jp DocumentRoot /var/www/html/virtual.jp RewriteEngine On RewriteCond %{HTTP_HOST} ^www\.virtual\.jp RewriteRule ^(.*)$ http://virtual.jp/$1 [R=301,L] ErrorLog logs/virtual.jp-error_log CustomLog logs/virtual.jp-access_log combined env=!no_log </VirtualHost>
s54再起動します。
[root@www ~]# 54_1systemctl restart httpd
s55
テストページを作成します。
[root@www ~]# 55_1echo test >> /var/www/html/virtual.jp/index.html
s56Web作動確認サイトで複数ドメインの作動確認をします。
複数ドメイン:http://virtual.jp
s57
サーバー証明書を取得します。
[root@www ~]# 57_1certbot certonly --webroot -w /var/www/html/virtual.jp -m webmaster@fedoraserver.jp -d virtual.jp --agree-tos
s58
メインドメイン設定を表示します。
[root@www ~]# 58_1vi /etc/httpd/conf.d/virtualhost-00-fedoraserver.jp.conf
s59行番号を非表示にします。
59_1:set nonumber
s60SSLの設定項目をコピーしてメモ帳などに貼り付け、設定変更して保存します。
コピー範囲:<VirtualHost _default_:443>~</VirtualHost>
変更内容:<VirtualHost _default_:443> → <VirtualHost *:443>
<VirtualHost 60_1*:443>
# General setup for the virtual host, inherited from global configuration
DocumentRoot "60_2/var/www/html/virtual.jp"
ServerName 60_3virtual.jp:443
# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
ErrorLog logs/ssl_error_log
TransferLog logs/ssl_access_log
LogLevel warn
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA
# Speed-optimized SSL Cipher configuration:
# If speed is your main concern (on busy HTTPS servers e.g.),
# you might want to force clients to specific, performance
# optimized ciphers. In this case, prepend those ciphers
# to the SSLCipherSuite list, and enable SSLHonorCipherOrder.
# Caveat: by giving precedence to RC4-SHA and AES128-SHA
# (as in the example below), most connections will no longer
# have perfect forward secrecy - if the server's key is
# compromised, captures of past or future traffic must be
# considered compromised, too.
#SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5
#SSLHonorCipherOrder on
# Server Certificate:
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that a kill -HUP will prompt again. A new
# certificate can be generated using the genkey(1) command.
SSLCertificateFile 61_1/etc/letsencrypt/live/virtual.jp/cert.pem
# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
SSLCertificateKeyFile 62_1/etc/letsencrypt/live/virtual.jp/privkey.pem
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
SSLCertificateChainFile 63_1/etc/letsencrypt/live/virtual.jp/chain.pem
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
#SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location>
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<Files ~ "\.(cgi|shtml|phtml|php3?)$">
SSLOptions +StdEnvVars
</Files>
<Directory "/var/www/cgi-bin">
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
BrowserMatch "MSIE [2-5]" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
# Per-Server Logging:
# The home of a custom SSL log file. Use this when you want a
# compact non-error SSL logfile on a virtual host basis.
CustomLog logs/ssl_request_log \
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
</VirtualHost>
s64ファイルを設定します。
[root@www ~]# 64_1vi /etc/httpd/conf.d/virtualhost-virtual.jp.conf
s65先に保存したものを最終行に貼り付けます。
<VirtualHost *:80> ServerName virtual.jp DocumentRoot /var/www/html/virtual.jp RewriteEngine On RewriteCond %{HTTP_HOST} ^www\.virtual\.jp RewriteRule ^(.*)$ http://virtual.jp/$1 [R=301,L] ErrorLog logs/virtual.jp-error_log CustomLog logs/virtual.jp-access_log combined env=!no_log </VirtualHost> <VirtualHost *:443> # General setup for the virtual host, inherited from global configuration DocumentRoot "/var/www/html/virtual.jp" ServerName virtual.jp:443 # Use separate log files for the SSL virtual host; note that LogLevel # is not inherited from httpd.conf. ErrorLog logs/ssl_error_log TransferLog logs/ssl_access_log LogLevel warn # SSL Engine Switch: # Enable/Disable SSL for this virtual host. SSLEngine on # SSL Protocol support: # List the enable protocol levels with which clients will be able to # connect. Disable SSLv2 access by default: SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2 # SSL Cipher Suite: # List the ciphers that the client is permitted to negotiate. # See the mod_ssl documentation for a complete list. SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA # Speed-optimized SSL Cipher configuration: # If speed is your main concern (on busy HTTPS servers e.g.), # you might want to force clients to specific, performance # optimized ciphers. In this case, prepend those ciphers # to the SSLCipherSuite list, and enable SSLHonorCipherOrder. # Caveat: by giving precedence to RC4-SHA and AES128-SHA # (as in the example below), most connections will no longer # have perfect forward secrecy - if the server's key is # compromised, captures of past or future traffic must be # considered compromised, too. #SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5 #SSLHonorCipherOrder on # Server Certificate: # Point SSLCertificateFile at a PEM encoded certificate. If # the certificate is encrypted, then you will be prompted for a # pass phrase. Note that a kill -HUP will prompt again. A new # certificate can be generated using the genkey(1) command. SSLCertificateFile /etc/letsencrypt/live/virtual.jp/cert.pem # Server Private Key: # If the key is not combined with the certificate, use this # directive to point at the key file. Keep in mind that if # you've both a RSA and a DSA private key you can configure # both in parallel (to also allow the use of DSA ciphers, etc.) SSLCertificateKeyFile /etc/letsencrypt/live/virtual.jp/privkey.pem # Server Certificate Chain: # Point SSLCertificateChainFile at a file containing the # concatenation of PEM encoded CA certificates which form the # certificate chain for the server certificate. Alternatively # the referenced file can be the same as SSLCertificateFile # when the CA certificates are directly appended to the server # certificate for convinience. SSLCertificateChainFile /etc/letsencrypt/live/virtual.jp/chain.pem # Certificate Authority (CA): # Set the CA certificate verification path where to find CA # certificates for client authentication or alternatively one # huge file containing all of them (file must be PEM encoded) #SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt # Client Authentication (Type): # Client certificate verification type and depth. Types are # none, optional, require and optional_no_ca. Depth is a # number which specifies how deeply to verify the certificate # issuer chain before deciding the certificate is not valid. #SSLVerifyClient require #SSLVerifyDepth 10 # Access Control: # With SSLRequire you can do per-directory access control based # on arbitrary complex boolean expressions containing server # variable checks and other lookup directives. The syntax is a # mixture between C and Perl. See the mod_ssl documentation # for more details. #<Location /> #SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \ # and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \ # and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \ # and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \ # and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \ # or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/ #</Location> # SSL Engine Options: # Set various options for the SSL engine. # o FakeBasicAuth: # Translate the client X.509 into a Basic Authorisation. This means that # the standard Auth/DBMAuth methods can be used for access control. The # user name is the `one line' version of the client's X.509 certificate. # Note that no password is obtained from the user. Every entry in the user # file needs this password: `xxj31ZMTZzkVA'. # o ExportCertData: # This exports two additional environment variables: SSL_CLIENT_CERT and # SSL_SERVER_CERT. These contain the PEM-encoded certificates of the # server (always existing) and the client (only existing when client # authentication is used). This can be used to import the certificates # into CGI scripts. # o StdEnvVars: # This exports the standard SSL/TLS related `SSL_*' environment variables. # Per default this exportation is switched off for performance reasons, # because the extraction step is an expensive operation and is usually # useless for serving static content. So one usually enables the # exportation for CGI and SSI requests only. # o StrictRequire: # This denies access when "SSLRequireSSL" or "SSLRequire" applied even # under a "Satisfy any" situation, i.e. when it applies access is denied # and no other module can change it. # o OptRenegotiate: # This enables optimized SSL connection renegotiation handling when SSL # directives are used in per-directory context. #SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire <Files ~ "\.(cgi|shtml|phtml|php3?)$"> SSLOptions +StdEnvVars </Files> <Directory "/var/www/cgi-bin"> SSLOptions +StdEnvVars </Directory> # SSL Protocol Adjustments: # The safe and default but still SSL/TLS standard compliant shutdown # approach is that mod_ssl sends the close notify alert but doesn't wait for # the close notify alert from client. When you need a different shutdown # approach you can use one of the following variables: # o ssl-unclean-shutdown: # This forces an unclean shutdown when the connection is closed, i.e. no # SSL close notify alert is send or allowed to received. This violates # the SSL/TLS standard but is needed for some brain-dead browsers. Use # this when you receive I/O errors because of the standard approach where # mod_ssl sends the close notify alert. # o ssl-accurate-shutdown: # This forces an accurate shutdown when the connection is closed, i.e. a # SSL close notify alert is send and mod_ssl waits for the close notify # alert of the client. This is 100% SSL/TLS standard compliant, but in # practice often causes hanging connections with brain-dead browsers. Use # this only for browsers where you know that their SSL implementation # works correctly. # Notice: Most problems of broken clients are also related to the HTTP # keep-alive facility, so you usually additionally want to disable # keep-alive for those clients, too. Use variable "nokeepalive" for this. # Similarly, one has to force some clients to use HTTP/1.0 to workaround # their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and # "force-response-1.0" for this. BrowserMatch "MSIE [2-5]" \ nokeepalive ssl-unclean-shutdown \ downgrade-1.0 force-response-1.0 # Per-Server Logging: # The home of a custom SSL log file. Use this when you want a # compact non-error SSL logfile on a virtual host basis. CustomLog logs/ssl_request_log \ "%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b" </VirtualHost>
s66
ホームネットワーク内でドメイン名で表示する様にBIND を設定します。
[root@www ~]# 66_1vi /etc/named.conf // // named.conf // // Provided by Red Hat bind package to configure the ISC BIND named(8) DNS // server as a caching only nameserver (as a localhost DNS resolver only). // // See /usr/share/doc/bind*/sample/ for example named configuration files. // // See the BIND Administrator's Reference Manual (ARM) for details about the // configuration located in /usr/share/doc/bind-{version}/Bv9ARM.html options { listen-on port 53 { any; }; listen-on-v6 port 53 { none; }; directory "/var/named"; dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; recursing-file "/var/named/data/named.recursing"; secroots-file "/var/named/data/named.secroots"; allow-query { localhost; 192.168.1.1/24; }; allow-transfer { localhost; 192.168.1.1/24; }; /* - If you are building an AUTHORITATIVE DNS server, do NOT enable recursion. - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion. - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface */ recursion yes; dnssec-enable yes; dnssec-validation yes; /* Path to ISC DLV key */ bindkeys-file "/etc/named.iscdlv.key"; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid"; session-keyfile "/run/named/session.key"; }; logging { channel default_debug { file "data/named.run"; severity dynamic; }; }; view "internal" { match-clients { localhost; 192.168.1.1/24; }; zone "." IN { type hint; file "named.ca"; }; zone "fedoraserver.jp" IN { type master; file "fedoraserver.jp.lan"; allow-update { none; }; }; 67_1 zone "virtual.jp" IN { type master; file "virtual.jp.lan"; allow-update { none; }; }; zone "1.168.192.in-addr.arpa" IN { type master; file "1.168.192.db"; allow-update { none; }; }; include "/etc/named.rfc1912.zones"; include "/etc/named.root.key"; };
s68
内部向け正引き情報ファイルを作成します。
[root@www ~]# 68_1vi /var/named/virtual.jp.lan 69_1$TTL 86400 @ IN SOA virtual.jp. root.virtual.jp. ( 2014071001 ;Serial 3600 ;Refresh 1800 ;Retry 604800 ;Expire 86400 ;Minimum TTL ) IN NS virtual.jp. IN MX 10 virtual.jp. @ IN A 192.168.1.3 * IN A 192.168.1.3
s70再起動します。
[root@www ~]# 70_1reboot
s71Web作動確認サイトで複数ドメインの作動確認をします。
複数ドメイン:https://virtual.jp
s50
サブドメイン用ディレクトリを作成します。
[root@www ~]# 50_1mkdir /var/www/html/sub.fedoraserver.jp
s51パーミッションを設定します。
[root@www ~]# 51_1chmod 777 /var/www/html/sub.fedoraserver.jp
s52サブドメイン用設定ファイルを作成します。
[root@www ~]# 52_1vi /etc/httpd/conf.d/virtualhost-sub.fedoraserver.jp.conf 52_2<VirtualHost *:80> ServerName sub.fedoraserver.jp DocumentRoot /var/www/html/sub.fedoraserver.jp RewriteEngine On RewriteCond %{HTTP_HOST} ^www\.sub\.fedoraserver\.jp RewriteRule ^(.*)$ http://sub.fedoraserver.jp/$1 [R=301,L] ErrorLog logs/sub.fedoraserver.jp-error_log CustomLog logs/sub.fedoraserver.jp-access_log combined env=!no_log </VirtualHost>
s53再起動します。
[root@www ~]# 53_1systemctl restart httpd
s54
テストページを作成します。
[root@www ~]# 54_1echo test >> /var/www/html/sub.fedoraserver.jp/index.html
s55Web作動確認サイトでサブドメインの作動確認をします。
サブドメイン:http://sub.fedoraserver.jp
s56
サーバー証明書を取得します。
[root@www ~]# 56_1certbot certonly --webroot -w /var/www/html/sub.fedoraserver.jp -m webmaster@fedoraserver.jp -d sub.fedoraserver.jp --agree-tos
s57
ファイルのバックアップを作成します。
[root@www ~]# 57_1cp /etc/httpd/conf.d/ssl.conf /etc/httpd/conf.d/ssl.conf.bk
s58ファイルを設定します。
[root@www ~]# 58_1vi /etc/httpd/conf.d/ssl.conf
s59行番号を非表示にします。
59_1:set nonumber
s60SSLの設定項目をコピーしてメモ帳などに貼り付け、設定変更して保存します。
コピー範囲:<VirtualHost _default_:443>~</VirtualHost>
変更内容:<VirtualHost _default_:443> → <VirtualHost *:443>
<VirtualHost 60_1*:443>
# General setup for the virtual host, inherited from global configuration
DocumentRoot "/var/www/html"
ServerName fedoraserver.jp:443
# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
ErrorLog logs/ssl_error_log
TransferLog logs/ssl_access_log
LogLevel warn
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA
# Speed-optimized SSL Cipher configuration:
# If speed is your main concern (on busy HTTPS servers e.g.),
# you might want to force clients to specific, performance
# optimized ciphers. In this case, prepend those ciphers
# to the SSLCipherSuite list, and enable SSLHonorCipherOrder.
# Caveat: by giving precedence to RC4-SHA and AES128-SHA
# (as in the example below), most connections will no longer
# have perfect forward secrecy - if the server's key is
# compromised, captures of past or future traffic must be
# considered compromised, too.
#SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5
#SSLHonorCipherOrder on
# Server Certificate:
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that a kill -HUP will prompt again. A new
# certificate can be generated using the genkey(1) command.
SSLCertificateFile /etc/letsencrypt/live/fedoraserver.jp/cert.pem
# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
SSLCertificateKeyFile /etc/letsencrypt/live/fedoraserver.jp/privkey.pem
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
SSLCertificateChainFile /etc/letsencrypt/live/fedoraserver.jp/chain.pem
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
#SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location>
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<Files ~ "\.(cgi|shtml|phtml|php3?)$">
SSLOptions +StdEnvVars
</Files>
<Directory "/var/www/cgi-bin">
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
BrowserMatch "MSIE [2-5]" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
# Per-Server Logging:
# The home of a custom SSL log file. Use this when you want a
# compact non-error SSL logfile on a virtual host basis.
CustomLog logs/ssl_request_log \
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
</VirtualHost>
s62ファイルを設定します。
[root@www ~]# 62_1vi /etc/httpd/conf.d/virtualhost-00-fedoraserver.jp.conf
s63先に保存したものを最終行に貼り付けます。
<VirtualHost *:80> ServerName fedoraserver.jp DocumentRoot /var/www/html/fedoraserver.jp RewriteEngine On RewriteCond %{HTTP_HOST} ^www\.fedoraserver\.jp RewriteRule ^(.*)$ http://fedoraserver.jp/$1 [R=301,L] </VirtualHost> <VirtualHost *:443> # General setup for the virtual host, inherited from global configuration DocumentRoot "/var/www/html" ServerName fedoraserver.jp:443 # Use separate log files for the SSL virtual host; note that LogLevel # is not inherited from httpd.conf. ErrorLog logs/ssl_error_log TransferLog logs/ssl_access_log LogLevel warn # SSL Engine Switch: # Enable/Disable SSL for this virtual host. SSLEngine on # SSL Protocol support: # List the enable protocol levels with which clients will be able to # connect. Disable SSLv2 access by default: SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2 # SSL Cipher Suite: # List the ciphers that the client is permitted to negotiate. # See the mod_ssl documentation for a complete list. SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA # Speed-optimized SSL Cipher configuration: # If speed is your main concern (on busy HTTPS servers e.g.), # you might want to force clients to specific, performance # optimized ciphers. In this case, prepend those ciphers # to the SSLCipherSuite list, and enable SSLHonorCipherOrder. # Caveat: by giving precedence to RC4-SHA and AES128-SHA # (as in the example below), most connections will no longer # have perfect forward secrecy - if the server's key is # compromised, captures of past or future traffic must be # considered compromised, too. #SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5 #SSLHonorCipherOrder on # Server Certificate: # Point SSLCertificateFile at a PEM encoded certificate. If # the certificate is encrypted, then you will be prompted for a # pass phrase. Note that a kill -HUP will prompt again. A new # certificate can be generated using the genkey(1) command. SSLCertificateFile /etc/letsencrypt/live/fedoraserver.jp/cert.pem # Server Private Key: # If the key is not combined with the certificate, use this # directive to point at the key file. Keep in mind that if # you've both a RSA and a DSA private key you can configure # both in parallel (to also allow the use of DSA ciphers, etc.) SSLCertificateKeyFile /etc/letsencrypt/live/fedoraserver.jp/privkey.pem # Server Certificate Chain: # Point SSLCertificateChainFile at a file containing the # concatenation of PEM encoded CA certificates which form the # certificate chain for the server certificate. Alternatively # the referenced file can be the same as SSLCertificateFile # when the CA certificates are directly appended to the server # certificate for convinience. SSLCertificateChainFile /etc/letsencrypt/live/fedoraserver.jp/chain.pem # Certificate Authority (CA): # Set the CA certificate verification path where to find CA # certificates for client authentication or alternatively one # huge file containing all of them (file must be PEM encoded) #SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt # Client Authentication (Type): # Client certificate verification type and depth. Types are # none, optional, require and optional_no_ca. Depth is a # number which specifies how deeply to verify the certificate # issuer chain before deciding the certificate is not valid. #SSLVerifyClient require #SSLVerifyDepth 10 # Access Control: # With SSLRequire you can do per-directory access control based # on arbitrary complex boolean expressions containing server # variable checks and other lookup directives. The syntax is a # mixture between C and Perl. See the mod_ssl documentation # for more details. #<Location /> #SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \ # and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \ # and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \ # and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \ # and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \ # or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/ #</Location> # SSL Engine Options: # Set various options for the SSL engine. # o FakeBasicAuth: # Translate the client X.509 into a Basic Authorisation. This means that # the standard Auth/DBMAuth methods can be used for access control. The # user name is the `one line' version of the client's X.509 certificate. # Note that no password is obtained from the user. Every entry in the user # file needs this password: `xxj31ZMTZzkVA'. # o ExportCertData: # This exports two additional environment variables: SSL_CLIENT_CERT and # SSL_SERVER_CERT. These contain the PEM-encoded certificates of the # server (always existing) and the client (only existing when client # authentication is used). This can be used to import the certificates # into CGI scripts. # o StdEnvVars: # This exports the standard SSL/TLS related `SSL_*' environment variables. # Per default this exportation is switched off for performance reasons, # because the extraction step is an expensive operation and is usually # useless for serving static content. So one usually enables the # exportation for CGI and SSI requests only. # o StrictRequire: # This denies access when "SSLRequireSSL" or "SSLRequire" applied even # under a "Satisfy any" situation, i.e. when it applies access is denied # and no other module can change it. # o OptRenegotiate: # This enables optimized SSL connection renegotiation handling when SSL # directives are used in per-directory context. #SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire <Files ~ "\.(cgi|shtml|phtml|php3?)$"> SSLOptions +StdEnvVars </Files> <Directory "/var/www/cgi-bin"> SSLOptions +StdEnvVars </Directory> # SSL Protocol Adjustments: # The safe and default but still SSL/TLS standard compliant shutdown # approach is that mod_ssl sends the close notify alert but doesn't wait for # the close notify alert from client. When you need a different shutdown # approach you can use one of the following variables: # o ssl-unclean-shutdown: # This forces an unclean shutdown when the connection is closed, i.e. no # SSL close notify alert is send or allowed to received. This violates # the SSL/TLS standard but is needed for some brain-dead browsers. Use # this when you receive I/O errors because of the standard approach where # mod_ssl sends the close notify alert. # o ssl-accurate-shutdown: # This forces an accurate shutdown when the connection is closed, i.e. a # SSL close notify alert is send and mod_ssl waits for the close notify # alert of the client. This is 100% SSL/TLS standard compliant, but in # practice often causes hanging connections with brain-dead browsers. Use # this only for browsers where you know that their SSL implementation # works correctly. # Notice: Most problems of broken clients are also related to the HTTP # keep-alive facility, so you usually additionally want to disable # keep-alive for those clients, too. Use variable "nokeepalive" for this. # Similarly, one has to force some clients to use HTTP/1.0 to workaround # their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and # "force-response-1.0" for this. BrowserMatch "MSIE [2-5]" \ nokeepalive ssl-unclean-shutdown \ downgrade-1.0 force-response-1.0 # Per-Server Logging: # The home of a custom SSL log file. Use this when you want a # compact non-error SSL logfile on a virtual host basis. CustomLog logs/ssl_request_log \ "%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b" </VirtualHost>
s64ファイルを設定します。
[root@www ~]# 64_1vi /etc/httpd/conf.d/ssl.conf
s65<VirtualHost _default_:443>~</VirtualHost>を削除します。
#
# When we also provide SSL we have to listen to the
# the HTTPS port in addition.
#
Listen 443 https
##
## SSL Global Context
##
## All SSL configuration in this context applies both to
## the main server and all SSL-enabled virtual hosts.
##
# Pass Phrase Dialog:
# Configure the pass phrase gathering process.
# The filtering dialog program (`builtin' is a internal
# terminal dialog) has to provide the pass phrase on stdout.
SSLPassPhraseDialog exec:/usr/libexec/httpd-ssl-pass-dialog
# Inter-Process Session Cache:
# Configure the SSL Session Cache: First the mechanism
# to use and second the expiring timeout (in seconds).
SSLSessionCache shmcb:/run/httpd/sslcache(512000)
SSLSessionCacheTimeout 300
# Pseudo Random Number Generator (PRNG):
# Configure one or more sources to seed the PRNG of the
# SSL library. The seed data should be of good random quality.
# WARNING! On some platforms /dev/random blocks if not enough entropy
# is available. This means you then cannot use the /dev/random device
# because it would lead to very long connection times (as long as
# it requires to make more entropy available). But usually those
# platforms additionally provide a /dev/urandom device which doesn't
# block. So, if available, use this one instead. Read the mod_ssl User
# Manual for more details.
SSLRandomSeed startup file:/dev/urandom 256
SSLRandomSeed connect builtin
#SSLRandomSeed startup file:/dev/random 512
#SSLRandomSeed connect file:/dev/random 512
#SSLRandomSeed connect file:/dev/urandom 512
#
# Use "SSLCryptoDevice" to enable any supported hardware
# accelerators. Use "openssl engine -v" to list supported
# engine names. NOTE: If you enable an accelerator and the
# server does not start, consult the error logs and ensure
# your accelerator is functioning properly.
#
SSLCryptoDevice builtin
#SSLCryptoDevice ubsec
#以下を削除
s66
先に保存したものをサブドメイン設定に修正します。
1行目:「_default_」を「*」に変更し、全てのドメインをサブドメインに変更します。
ドメイン:debianserver.jp
サブドメイン:sub.debianserver.jp
<VirtualHost 66_1*:443>
# General setup for the virtual host, inherited from global configuration
DocumentRoot "/var/www/html66_2/sub.fedoraserver.jp"
ServerName 66_3 sub.fedoraserver.jp:443
# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
ErrorLog logs/ssl_error_log
TransferLog logs/ssl_access_log
LogLevel warn
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA
# Speed-optimized SSL Cipher configuration:
# If speed is your main concern (on busy HTTPS servers e.g.),
# you might want to force clients to specific, performance
# optimized ciphers. In this case, prepend those ciphers
# to the SSLCipherSuite list, and enable SSLHonorCipherOrder.
# Caveat: by giving precedence to RC4-SHA and AES128-SHA
# (as in the example below), most connections will no longer
# have perfect forward secrecy - if the server's key is
# compromised, captures of past or future traffic must be
# considered compromised, too.
#SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5
#SSLHonorCipherOrder on
# Server Certificate:
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that a kill -HUP will prompt again. A new
# certificate can be generated using the genkey(1) command.
SSLCertificateFile /etc/letsencrypt/live/66_4sub.fedoraserver.jp/cert.pem
# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
SSLCertificateKeyFile /etc/letsencrypt/live/66_5sub.fedoraserver.jp/privkey.pem
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
SSLCertificateChainFile /etc/letsencrypt/live/66_6sub.fedoraserver.jp/chain.pem
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
#SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location>
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<Files ~ "\.(cgi|shtml|phtml|php3?)$">
SSLOptions +StdEnvVars
</Files>
<Directory "/var/www/cgi-bin">
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
BrowserMatch "MSIE [2-5]" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
# Per-Server Logging:
# The home of a custom SSL log file. Use this when you want a
# compact non-error SSL logfile on a virtual host basis.
CustomLog logs/ssl_request_log \
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
</VirtualHost>
s67ファイルを設定します。
[root@www ~]# 67_1vi /etc/httpd/conf.d/virtualhost-sub.fedoraserver.jp.conf
s68先に修正したものを最終行に貼り付けます。
<VirtualHost *:80> ServerName sub.fedoraserver.jp DocumentRoot /var/www/html/sub.fedoraserver.jp RewriteEngine On RewriteCond %{HTTP_HOST} ^www\.sub\.fedoraserver\.jp RewriteRule ^(.*)$ http://sub.fedoraserver.jp/$1 [R=301,L] ErrorLog logs/sub.fedoraserver.jp-error_log CustomLog logs/sub.fedoraserver.jp-access_log combined env=!no_log </VirtualHost> <VirtualHost *:443> # General setup for the virtual host, inherited from global configuration DocumentRoot "/var/www/html/sub.fedoraserver.jp" ServerName sub.fedoraserver.jp:443 # Use separate log files for the SSL virtual host; note that LogLevel # is not inherited from httpd.conf. ErrorLog logs/ssl_error_log TransferLog logs/ssl_access_log LogLevel warn # SSL Engine Switch: # Enable/Disable SSL for this virtual host. SSLEngine on # SSL Protocol support: # List the enable protocol levels with which clients will be able to # connect. Disable SSLv2 access by default: SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2 # SSL Cipher Suite: # List the ciphers that the client is permitted to negotiate. # See the mod_ssl documentation for a complete list. SSLCipherSuite HIGH:3DES:!aNULL:!MD5:!SEED:!IDEA # Speed-optimized SSL Cipher configuration: # If speed is your main concern (on busy HTTPS servers e.g.), # you might want to force clients to specific, performance # optimized ciphers. In this case, prepend those ciphers # to the SSLCipherSuite list, and enable SSLHonorCipherOrder. # Caveat: by giving precedence to RC4-SHA and AES128-SHA # (as in the example below), most connections will no longer # have perfect forward secrecy - if the server's key is # compromised, captures of past or future traffic must be # considered compromised, too. #SSLCipherSuite RC4-SHA:AES128-SHA:HIGH:MEDIUM:!aNULL:!MD5 #SSLHonorCipherOrder on # Server Certificate: # Point SSLCertificateFile at a PEM encoded certificate. If # the certificate is encrypted, then you will be prompted for a # pass phrase. Note that a kill -HUP will prompt again. A new # certificate can be generated using the genkey(1) command. SSLCertificateFile /etc/letsencrypt/live/sub.fedoraserver.jp/cert.pem # Server Private Key: # If the key is not combined with the certificate, use this # directive to point at the key file. Keep in mind that if # you've both a RSA and a DSA private key you can configure # both in parallel (to also allow the use of DSA ciphers, etc.) SSLCertificateKeyFile /etc/letsencrypt/live/sub.fedoraserver.jp/privkey.pem # Server Certificate Chain: # Point SSLCertificateChainFile at a file containing the # concatenation of PEM encoded CA certificates which form the # certificate chain for the server certificate. Alternatively # the referenced file can be the same as SSLCertificateFile # when the CA certificates are directly appended to the server # certificate for convinience. SSLCertificateChainFile /etc/letsencrypt/live/sub.fedoraserver.jp/chain.pem # Certificate Authority (CA): # Set the CA certificate verification path where to find CA # certificates for client authentication or alternatively one # huge file containing all of them (file must be PEM encoded) #SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt # Client Authentication (Type): # Client certificate verification type and depth. Types are # none, optional, require and optional_no_ca. Depth is a # number which specifies how deeply to verify the certificate # issuer chain before deciding the certificate is not valid. #SSLVerifyClient require #SSLVerifyDepth 10 # Access Control: # With SSLRequire you can do per-directory access control based # on arbitrary complex boolean expressions containing server # variable checks and other lookup directives. The syntax is a # mixture between C and Perl. See the mod_ssl documentation # for more details. #<Location /> #SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \ # and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \ # and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \ # and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \ # and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \ # or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/ #</Location> # SSL Engine Options: # Set various options for the SSL engine. # o FakeBasicAuth: # Translate the client X.509 into a Basic Authorisation. This means that # the standard Auth/DBMAuth methods can be used for access control. The # user name is the `one line' version of the client's X.509 certificate. # Note that no password is obtained from the user. Every entry in the user # file needs this password: `xxj31ZMTZzkVA'. # o ExportCertData: # This exports two additional environment variables: SSL_CLIENT_CERT and # SSL_SERVER_CERT. These contain the PEM-encoded certificates of the # server (always existing) and the client (only existing when client # authentication is used). This can be used to import the certificates # into CGI scripts. # o StdEnvVars: # This exports the standard SSL/TLS related `SSL_*' environment variables. # Per default this exportation is switched off for performance reasons, # because the extraction step is an expensive operation and is usually # useless for serving static content. So one usually enables the # exportation for CGI and SSI requests only. # o StrictRequire: # This denies access when "SSLRequireSSL" or "SSLRequire" applied even # under a "Satisfy any" situation, i.e. when it applies access is denied # and no other module can change it. # o OptRenegotiate: # This enables optimized SSL connection renegotiation handling when SSL # directives are used in per-directory context. #SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire <Files ~ "\.(cgi|shtml|phtml|php3?)$"> SSLOptions +StdEnvVars </Files> <Directory "/var/www/cgi-bin"> SSLOptions +StdEnvVars </Directory> # SSL Protocol Adjustments: # The safe and default but still SSL/TLS standard compliant shutdown # approach is that mod_ssl sends the close notify alert but doesn't wait for # the close notify alert from client. When you need a different shutdown # approach you can use one of the following variables: # o ssl-unclean-shutdown: # This forces an unclean shutdown when the connection is closed, i.e. no # SSL close notify alert is send or allowed to received. This violates # the SSL/TLS standard but is needed for some brain-dead browsers. Use # this when you receive I/O errors because of the standard approach where # mod_ssl sends the close notify alert. # o ssl-accurate-shutdown: # This forces an accurate shutdown when the connection is closed, i.e. a # SSL close notify alert is send and mod_ssl waits for the close notify # alert of the client. This is 100% SSL/TLS standard compliant, but in # practice often causes hanging connections with brain-dead browsers. Use # this only for browsers where you know that their SSL implementation # works correctly. # Notice: Most problems of broken clients are also related to the HTTP # keep-alive facility, so you usually additionally want to disable # keep-alive for those clients, too. Use variable "nokeepalive" for this. # Similarly, one has to force some clients to use HTTP/1.0 to workaround # their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and # "force-response-1.0" for this. BrowserMatch "MSIE [2-5]" \ nokeepalive ssl-unclean-shutdown \ downgrade-1.0 force-response-1.0 # Per-Server Logging: # The home of a custom SSL log file. Use this when you want a # compact non-error SSL logfile on a virtual host basis. CustomLog logs/ssl_request_log \ "%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b" </VirtualHost>
s70再起動します。
[root@www ~]# 70_1systemctl restart httpd
s71Web作動確認サイトでサブドメインの作動確認をします。
サブドメイン:https://sub.fedoraserver.jp
AWStatsをインストールします。
[root@www ~]# dnf -y install awstats
自動作成されているawstats.fedoraserver.jp.conf を設定します。
[root@www ~]# vi /etc/awstats/awstats.fedoraserver.jp.conf
125行目:変更します。
LogFormat=1
156行目:ホスト名を設定します。
SiteDomain="fedoraserver.jp"
171行目:除外したドメイン名やIPアドレスを追記します。
HostAliases="localhost 127.0.0.1 REGEX[^.*fedoraserver\.jp$] REGEX[^192\.168\.1\.]"
awstats.confを設定します。
[root@www ~]# vi /etc/httpd/conf.d/awstats.conf
30行目:アクセス許可IPを追記します。
Require ip 192.168.1.1/24
再起動します。
[root@www ~]# systemctl restart httpd
1時間毎に自動更新する設定をします。
[root@www ~]# /usr/share/awstats/wwwroot/cgi-bin/awstats.pl -config=fedoraserver.jp -update
Web ブラウザを起動し、「http://fedoraserver.jp/awstats/awstats.pl」にアクセスして、作動確認します。
pflogsumm をインストールします。
[root@www ~]# dnf -y install postfix-perl-scripts
メールログのサマリーを出力します。
[root@www ~]# perl /usr/sbin/pflogsumm -d yesterday /var/log/maillog Postfix log summaries for Jul 29 Grand Totals ------------ messages 8 received 8 delivered 2 forwarded 1 deferred (1 deferrals) 0 bounced 0 rejected (0%) 0 reject warnings 0 held 0 discarded (0%) 2428k bytes received 2429k bytes delivered 3 senders 2 sending hosts/domains 2 recipients 2 recipient hosts/domains Per-Hour Traffic Summary ------------------------ time received delivered deferred bounced rejected -------------------------------------------------------------------- 0000-0100 0 0 0 0 0 0100-0200 0 0 0 0 0 0200-0300 0 0 0 0 0 …
root宛てにメール送信する設定をします。
[root@www ~]# crontab -e
毎日午前1時にメール送信する設定をします。
[root@www ~]# 00 01 * * * perl /usr/sbin/pflogsumm -e -d yesterday /var/log/maillog | mail -s 'Logwatch for Postfix' root
Nagiosに必要なgd-develをインストールします。
root@www:~# dnf -y install gd-devel
nagiosユーザーを作成します。
root@www:~# useradd -d /usr/local/nagios/ -M nagios
Nagiosをダウンロードします。
root@www:~# wget https://github.com/NagiosEnterprises/nagioscore/releases/download/nagios-4.4.6/nagios-4.4.6.tar.gz
Nagiosを展開します。
root@www:~# tar zxvf nagios-4.4.6.tar.gz
Nagios展開先ディレクトリへ移動します。
root@www:~# cd nagios-4.4.6
patchをインストールします。
root@www:~# dnf -y install patch
Nagios日本語化パッチをダウンロードします。
root@www:nagios-4.4.6# wget http://ftp.momo-i.org/pub/security/nagios/patches/nagios-jp-4.4.6.patch.gz
Nagios日本語化パッチを施行します。
root@www:nagios-4.4.6# gzip -dc nagios-jp-4.4.6.patch.gz |patch -p1
Nagiosをインストールします。
root@www:nagios-4.4.6# ./configure && make all && make fullinstall && make install-config
ディレクトリを抜けます。
root@www:nagios-4.4.6# cd
Nagios展開先ディレクトリを削除します。
root@www:~# rm -rf nagios-4.4.6
ダウンロードしたファイルを削除します。
root@www:~# rm -f nagios-4.4.6.tar.gz
Nagiosプラグインをダウンロードします。
root@www:~# wget https://github.com/nagios-plugins/nagios-plugins/releases/download/release-2.3.3/nagios-plugins-2.3.3.tar.gz
Nagiosプラグインを展開します。
root@www:~# tar zxvf nagios-plugins-2.3.3.tar.gz
Nagiosプラグイン展開先ディレクトリへ移動します。
root@www:~# cd nagios-plugins-2.3.3
Nagiosプラグインをインストールします。
root@www:nagios-plugins-2.3.3# ./configure && make && make install
ディレクトリを抜けます。
root@www:nagios-plugins-2.3.3# cd
Nagiosプラグイン展開先ディレクトリを削除します。
root@www:~# rm -rf nagios-plugins-2.3.3
ダウンロードしたファイルを削除します。
root@www:~# rm -f nagios-plugins-2.3.3.tar.gz
nagios.cfgを設定します。
root@www:~# vi /usr/local/nagios/etc/nagios.cfg
51行目:行頭の「#」を削除してコメント解除し、サーバー監視設定有効化を設定します。
cfg_dir=/usr/local/nagios/etc/servers
1096:行目:日付書式をYYYY-MM-DD HH:MM:SSにするを設定します。
date_format=iso8601
サーバー監視設定ファイル格納ディレクトリを作成します。
root@www:~# mkdir /usr/local/nagios/etc/servers
contacts.cfgを設定します。
root@www:~# vi /usr/local/nagios/etc/objects/contacts.cfg
32行目:管理者メールアドレスを指定を設定します。
define contact{ contact_name nagiosadmin ; Short name of user use generic-contact ; Inherit default values from generic-contact template (defined above) alias Nagios Admin ; Full name of user email root@localhost }
localhost.cfgを設定します。
root@www:~# vi /usr/local/nagios/etc/objects/localhost.cfg
144行目:SSH状態変化時に通知するを設定します。
define service{ use local-service ; Name of service template to use host_name localhost service_description SSH check_command check_ssh notifications_enabled 1 }
158行目:SSH状態変化時に通知するを設定します。
define service{ use local-service ; Name of service template to use host_name localhost service_description HTTP check_command check_http notifications_enabled 1 }
commands.cfgを設定します。
root@www:~# vi /usr/local/nagios/etc/objects/commands.cfg
29行目:nkfコマンドのメール本文文字化け対策を設定します。
# 'notify-host-by-email' command definition
define command{
command_name notify-host-by-email
command_line /usr/bin/printf "%b" "***** Nagios *****\n\nNotification Type: $NOTIFICATIONTYPE$\nHost: $HOSTNAME$\nState: $HOSTSTATE$\nAddress: $HOSTADDRESS$\nInfo: $HOSTOUTPUT$\n\nDate/Time: $LONGDATETIME$\n" | /usr/bin/nkf -j | /usr/bin/mail -s "** $NOTIFICATIONTYPE$ Host Alert: $HOSTNAME$ is $HOSTSTATE$ **" $CONTACTEMAIL$
}
37行目:nkfコマンドのメール本文文字化け対策を設定します。
# 'notify-service-by-email' command definition
define command{
command_name notify-service-by-email
command_line /usr/bin/printf "%b" "***** Nagios *****\n\nNotification Type: $NOTIFICATIONTYPE$\n\nService: $SERVICEDESC$\nHost: $HOSTALIAS$\nAddress: $HOSTADDRESS$\nState: $SERVICESTATE$\n\nDate/Time: $LONGDATETIME$\n\nAdditional Info:\n\n$SERVICEOUTPUT$\n" | /usr/bin/nkf -j | /usr/bin/mail -s "** $NOTIFICATIONTYPE$ Service Alert: $HOSTALIAS$/$SERVICEDESC$ is $SERVICESTATE$ **" $CONTACTEMAIL$
}
Nagios用Apache httpd設定ファイルを設定します。
root@www:~# vi /etc/httpd/conf.d/nagios.conf
16行目:追記します。
<RequireAny>
17行目:行頭に「#」を追記してコメント化し、内部からのみアクセス可能にする設定をします。
# Require all granted
19行目:内部ネットワーク(192.168.1.1/24)からのみアクセス可能にする設定をします。
Require ip 192.168.1.1/24
20行目:追記します。
</RequireAny>
49行目:追記します。
<RequireAny>
50行目:行頭に「#」を追記してコメント化し、内部からのみアクセス可能にする設定をします。
# Require all granted
52行目:内部ネットワーク(192.168.1.1/24)からのみアクセス可能にする設定をします。
Require ip 192.168.1.1/24
53行目:追記します。
</RequireAny>
Webサーバー設定反映を設定します。
root@www:~# systemctl restart httpd
Nagios管理ユーザー(nagiosadmin)を作成します。
root@www:~# htpasswd -c /usr/local/nagios/etc/htpasswd.users nagiosadmin
パスワードを設定します。
New password:
Re-type new password:
Adding password for user nagiosadmin
起動します。
root@www:~# systemctl restart nagios
Webブラウザを起動し、「http://ubuntuserver.jp/nagios/」にアクセスし、管理ユーザー:nagiosadmin、登録済パスワードでログインして動作確認をします。
外部からWebアクセスできるようにします。
[root@www ~]# vi /etc/httpd/conf.d/virtualhost-00-fedoraserver.jp.conf <VirtualHost *:80> ServerName fedoraserver.jp DocumentRoot /var/www/html ServerAlias mail.fedoraserver.jp RewriteEngine On RewriteCond %{HTTP_HOST} ^www\.fedoraserver\.jp RewriteRule ^(.*)$ http://fedoraserver.jp/$1 [R=301,L] </VirtualHost>
Postfixをインストールをします。
[root@www ~]# dnf install postfix
Postfixを設定します。
[root@www ~]# vi /etc/postfix/main.cf
96行目:メールサーバードメイン名の指定を追記します。
myhostname = mail.fedoraserver.jp
103行目:ドメイン名の指定を追記します。
mydomain = fedoraserver.jp
119行目:送信元メールアドレスにドメイン名の指定を追記します。
myorigin = $mydomain
135行目:外部からのメール受信を許可する設定に変更します。
inet_interfaces = all
183行目:ドメインメールを受信する設定に変更します。
mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain
439行目:メール格納形式をMaildir形式にする設定を追記します。
home_mailbox = Maildir/
593行目:メールサーバーソフト名の隠蔽化する設定を追記します。
smtpd_banner = $myhostname ESMTP unknown
SMTP認証の設定を最終行へ追加します。
smtpd_sasl_auth_enable = yes
smtpd_recipient_restrictions =
permit_mynetworks
permit_sasl_authenticated
reject_unauth_destination
受信メールサイズを10MB=10*1024*1024に制限する設定を最終行へ追記します。
message_size_limit = 10485760
master.cfを設定します。
[root@www ~]# vi /etc/postfix/master.cf
17行目:行頭の「#」を削除してコメント解除します。
submission inet n - n - - smtpd
20行目:行頭の「#」を削除してコメント解除します。
-o smtpd_sasl_auth_enable=yes
cyrus-saslをインストールします。
[root@www ~]# dnf install cyrus-sasl cyrus-sasl-plain
起動します。
[root@www ~]# systemctl start saslauthd
自動起動設定します。
[root@www ~]# systemctl enable saslauthd
新規ユーザー追加時に自動でMaildir形式メールボックス作成する設定をします。
[root@www ~]# mkdir -p /etc/skel/Maildir/{new,cur,tmp}
メールボックスパーミッションを設定します。
[root@www ~]# chmod -R 700 /etc/skel/Maildir/
起動します。
[root@www ~]# systemctl restart postfix
現在のユーザーのMaildir形式メールボックス作成する設定をします。
[root@www ~]# wget https://rcg.jp/perfect_maildir/perfect_maildir.pl -O /usr/local/bin/perfect_maildir.pl [root@www ~]# chmod +x /usr/local/bin/perfect_maildir.pl
Maildir変換に必要なPerlのTimeDateモジュールインストールします。
[root@www ~]# dnf -y install perl-TimeDate
Postfixを停止します。
[root@www ~]# systemctl stop postfix
Maildir一括変換スクリプトを作成します。
[root@www ~]# vi migrate-maildir.sh #!/bin/bash # #Maildir一括変換スクリプト # #メールボックス=>Maildir形式変換スクリプト #http://perfectmaildir.home-dn.net/ FOLDERCONVERT=/usr/local/bin/perfect_maildir.pl #一般ユーザリスト USERLIST=`ls /home/` #ログ MIGRATELOG=/tmp/migrate-maildir.log rm -f $MIGRATELOG #引数(変換元メールボックス形式)チェック if [ "$1" != "mbox" ] && [ "$1" != "Mailbox" ]; then echo "Usage: migrate-maildir.sh {mbox|Mailbox}" exit fi #一般ユーザメールボックス移行 for user in $USERLIST; do if [ "$1" = "mbox" ]; then inbox="/var/spool/mail/${user}" else inbox="/home/${user}/Mailbox" fi if [ -f "${inbox}" ]; then newdir="/home/${user}/Maildir/" mkdir -p "$newdir" mkdir -p "$newdir"/cur mkdir -p "$newdir"/new mkdir -p "$newdir"/tmp chmod -R 700 "${newdir}" $FOLDERCONVERT "$newdir" < "${inbox}" >> $MIGRATELOG 2>&1 chown -R ${user}. "$newdir" find "$newdir" -type f -exec chmod 600 {} \; fi done #rootユーザメールボックス移行 user="root" if [ "$1" = "mbox" ]; then inbox="/var/spool/mail/${user}" else inbox="/${user}/Mailbox" fi if [ -f "${inbox}" ]; then newdir="/${user}/Maildir/" mkdir -p "$newdir" mkdir -p "$newdir"/cur mkdir -p "$newdir"/new mkdir -p "$newdir"/tmp chmod -R 700 "${newdir}" $FOLDERCONVERT "$newdir" < "${inbox}" >> $MIGRATELOG 2>&1 chown -R ${user}. "$newdir" find "$newdir" -type f -exec chmod 600 {} \; fi [ -a $MIGRATELOG ] && cat $MIGRATELOG;rm -f $MIGRATELOG
一括変換スクリプトを実行します。
[root@www ~]# sh migrate-maildir.sh mbox
Maildir一括変換スクリプトを削除します。
[root@www ~]# rm -f migrate-maildir.sh
Maildir変換ツールを削除します。
[root@www ~]# rm -f /usr/local/bin/perfect_maildir.pl
起動します。
[root@www ~]# systemctl restart postfix
webmasterユーザーをメール使用する場合は「/etc/aliases」を変更します。
[root@www ~]# vi /etc/aliases
行頭に#を追加して転送を無効にします。
#webmaster: root
転送設定を反映します。
[root@www ~]# newaliases
ルーターの設定で、TCP25番、TCP587番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
こちらのサイトで「ホスト名(fedoraserver.jp)」、「ポート番号(25,587)」の開放確認をします。
メールサーバーのOP25B対策として送信メールをGmailを経由して送信するように設定します。
Postfixを設定します。
[root@www ~]# vi /etc/postfix/main.cf
以下を最終行へ追加します。
relayhost = [smtp.gmail.com]:587
smtp_use_tls = yes
smtp_sasl_auth_enable = yes
smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd
smtp_sasl_tls_security_options = noanonymous
smtp_sasl_mechanism_filter = plain
SMTP認証情報を設定します。
[root@www ~]# echo [smtp.gmail.com]:587 Gmailアドレス:Gmailパスワード > /etc/postfix/sasl_passwd
root以外参照できないようにパーミッション変更します。
[root@www ~]# chmod 640 /etc/postfix/sasl_passwd
SMTP認証情報をデータベース化します。
[root@www ~]# postmap /etc/postfix/sasl_passwd
Postfixを再起動します。
[root@www ~]# systemctl reload postfix
root宛メールを転送します。
[root@www ~]# vi /etc/aliases
最終行に追記します。
# Person who should get root's mail #root: marc root: 転送用メールアドレス
転送設定を反映します。
[root@www ~]# newaliases
テストメールをroot宛に送信します。
[root@www ~]# echo test|sendmail root
先にThunderbirdへGmail(送信用メール)を設定します。
Thunderbirdを起動し、送信用メールアドレスで「ブロックされたログインについてご確認ください」を開き、「安全性の低いアプリへのアクセスを許可」をクリックします。
ブラウザでGmailにログインします。
右上のユーザーアイコンを右クリック→「Googleアカウントの管理」→「セキュリティ」→「安全性の低いアプリのアクセス」でアクセスを有効にします。
先にThunderbirdへGmail(転送用メール)を設定します。
Thunderbird(Gmail)のroot宛の転送用メールアドレスで受信を確認します。
[root@www ~]# dnf -y install dovecot
dovecot.confを設定します。
[root@www ~]# vi /etc/dovecot/dovecot.conf
24行目:行頭「#」を削除してコメント解除します。
protocols = imap pop3 lmtp submission
30行目:行頭「#」を削除してコメント解除し、IPv6を無効にする設定に変更します。
listen = *
10-mail.confを設定します。
[root@www ~]# vi /etc/dovecot/conf.d/10-mail.conf
31行目:メール格納形式をMaildir形式にする設定を追記します。
mail_location = maildir:~/Maildir
10-auth.confを設定します。
[root@www ~]# vi /etc/dovecot/conf.d/10-auth.conf
11行目:プレインテキスト認証を許可する設定を追記します。
disable_plaintext_auth = no
10-ssl.confを設定します。
[root@www ~]# vi /etc/dovecot/conf.d/10-ssl.conf
8行目:SSL接続を無効にする設定に変更します。
ssl = no
起動します。
[root@www ~]# systemctl start dovecot
自動起動を設定します。
[root@www ~]# systemctl enable dovecot
ルーターの設定で、TCP110番またはTCP143番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
こちらのサイトで「ホスト名(fedoraserver.jp)」、「ポート番号(110または143)」の開放確認をします。
ユーザーを追加します。(ユーザー例:fedora)
[root@www ~]# useradd fedora
パスワードを設定します。
[root@www ~]# passwd fedora Changing password for user fedora. New UNIX password: Retype new UNIX password:
sshd_configを編集します。
[root@www ~]# vi /etc/ssh/sshd_config
65行目:「no」→「yes」に変更します。
PasswordAuthentication yes
SSHを再起動します。
[root@www ~]# systemctl restart sshd
TeraTermにfedoraで新しい接続をします。
SSHサーバー公開鍵認証方式接続の設定をします。
main.cfを開きます。
[root@www ~]# vi /etc/postfix/main.cf
665行目:sendmailパスの確認します。
sendmail_path = /usr/sbin/sendmail.postfix
Thunderbirdを起動し、メールをクリックします。
あなたのお名前、メールアドレス(fedora@fedoraserver.jp)、パスワードを入力し、「続ける」をクリックします。
「手動設定」をクリックします。
| サーバーのホスト名 | ポート番号 | SSL | 認証方式 | ||
| 受信サーバー | POP3 | mail.fedoraserver.jp | 110 | 接続の保護なし | 通常のパスワード認証 |
| 送信サーバー | SMTP | mail.fedoraserver.jp | 587 | 接続の保護なし | 通常のパスワード認証 |
上の表を参考にして設定し、「完了」をクリックします。
「接続する上での危険性を理解しました」を選択して「完了」をクリックします。
Certbotをインストールします。
[root@www ~]# dnf -y install certbot
証明書を取得します。
ドキュメントルート:/var/www/html/
メールアドレス:webmaster@fedoraserver.jp
メールサーバー名:mail.fedoraserver.jp
[root@www ~]# certbot certonly --webroot -w /var/www/html/ -m webmaster@fedoraserver.jp -d mail.fedoraserver.jp --agree-tos
証明書自動更新を設定します。
[root@www ~]# vi /etc/cron.d/letsencrypt
下記を追記します。
00 16 * * 2 root /usrobin/certbot renew --post-hook "service httpd restart"
main.cfを設定します。
[root@www ~]# vi /etc/postfix/main.cf
下記を最終行に追記します。
smtp_tls_security_level = may
smtpd_tls_security_level = may
smtpd_tls_cert_file = /etc/letsencrypt/live/mail.fedoraserver.jp/fullchain.pem
smtpd_tls_key_file = /etc/letsencrypt/live/mail.fedoraserver.jp/privkey.pem
smtpd_tls_session_cache_database = btree:/var/lib/postfix/smtpd_scache
tls_high_cipherlist = kEECDH:+kEECDH+SHA:kEDH:+kEDH+SHA:+kEDH+CAMELLIA:kECDH:+kECDH+SHA:kRSA:+kRSA+SHA:+kRSA+CAMELLIA:!aNULL:!eNULL:!SSLv2:!RC4:!MD5:!DES:!EXP:!SEED:!IDEA:!3DES
smtp_tls_ciphers = high
smtpd_tls_ciphers = high
smtpd_tls_mandatory_ciphers = high
smtpd_tls_mandatory_protocols=!SSLv2,!SSLv3
smtp_tls_mandatory_protocols=!SSLv2,!SSLv3
smtpd_tls_protocols=!SSLv2,!SSLv3
smtp_tls_protocols=!SSLv2,!SSLv3
master.cfを設定します。
[root@www ~]# vi /etc/postfix/master.cf
17行目:行頭に「#」を追加してコメント化し、SUBMISSIONポートを無効化します。
#submission inet n - n - - smtpd
20行目:行頭に「#」を追加してコメント化し、SUBMISSIONポートのSMTP認証を無効化します。
# -o smtpd_sasl_auth_enable=yes
29行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
smtps inet n - n - - smtpd
31行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
-o smtpd_tls_wrappermode=yes
32行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
-o smtpd_sasl_auth_enable=yes
45行目:行頭の「#」を削除してコメント解除し、SMTPSを有効化します。
tlsmgr unix - - n 300 1 tlsmgr
再起動します。
[root@www ~]# systemctl restart postfix
ルーターの設定で、TCP465番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
こちらのサイトで「ホスト名(mail.fedoraserver.jp)」、「ポート番号(465)」の開放確認をします。
ルーターの設定で、TCP587番ポートを閉鎖します。(設定方法はご自身の環境に合わせて調べてください。)
こちらのサイトで「ホスト名(mail.fedoraserver.jp)」、「ポート番号(587)」の開放されていないことを確認をします。
10-auth.confを設定します。
[root@www ~]# vi /etc/dovecot/conf.d/10-ssl.conf
8行目:SSL接続を有効にする設定に変更します。
ssl = yes
14行目:サーバー証明書+中間証明書を指定します。
ssl_cert = </etc/letsencrypt/live/mail.fedoraserver.jp/fullchain.pem
15行目:秘密鍵を指定します。
ssl_key = </etc/letsencrypt/live/mail.fedoraserver.jp/privkey.pem
再起動します。
[root@www ~]# systemctl restart dovecot
ルーターの設定で、TCP995番またはTCP993番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
こちらのサイトで「ホスト名(mail.fedoraserver.jp)」、「ポート番号(995または993)」の開放確認をします。
Thunderbirdを起動し、メールアドレスを選択し、「このアカウントの設定を表示する」をクリックします。
「サーバー設定」をクリックし、「接続の保護」で「SSL/TLS」を選択します。
「送信(SMTP)サーバー」をクリックし、SMTPサーバーを選択して「編集」をクリックします。
「ポート番号」に「465」を入力し、「接続の保護」で「SSL/TLS」を選択して、「OK」をクリックします。
「OK」をクリックします。
Amavisd および Clamav Server をインストールします。
[root@www ~]# dnf -y install amavisd-new clamd perl-Digest-SHA1 perl-IO-stringy
amavisd.confを設定します。
[root@www ~]# vi /etc/amavisd/amavisd.conf
23行目:ドメイン名を設定します。
$mydomain = 'fedoraserver.jp';
155行目:行頭の「#」を削除してコメント解除し、メールサーバーを設定します。
$myhostname = 'mail.fedoraserver.jp';
157、158行目:行頭の「#」を削除してコメント解除します。
$notify_method = 'smtp:[127.0.0.1]:10025';
$forward_method = 'smtp:[127.0.0.1]:10025';
scan.confを設定します。
[root@www ~]# vi /etc/clamd.d/scan.conf
8行目:行頭に「#」を追加してコメント化します。
#Example
14行目:行頭の「#」を削除してコメント解除します。
LogFile /var/log/clamd.scan
77行目:行頭の「#」を削除してコメント解除します。
PidFile /var/run/clamd.scan/clamd.pid
81行目:行頭の「#」を削除してコメント解除します。
TemporaryDirectory /var/tmp
96行目:行頭の「を」削除してコメント解除します。
LocalSocket /var/run/clamd.scan/clamd.sock
起動します。
[root@www ~]# touch /var/log/clamd.scan [root@www ~]# chown clamscan. /var/log/clamd.scan
自動起動を設定します。
[root@www ~]# systemctl enable --now clamd@scan amavisd
main.cfの設定です。
[root@www ~]# vi /etc/postfix/main.cf
最終行に追記します。
content_filter=smtp-amavis:[127.0.0.1]:10024
master.cfの設定です。
[root@www ~]# vi /etc/postfix/master.cf
最終行に追記します。
smtp-amavis unix - - n - 2 smtp
-o smtp_data_done_timeout=1200
-o smtp_send_xforward_command=yes
-o disable_dns_lookups=yes
127.0.0.1:10025 inet n - n - - smtpd
-o content_filter=
-o local_recipient_maps=
-o relay_recipient_maps=
-o smtpd_restriction_classes=
-o smtpd_client_restrictions=
-o smtpd_helo_restrictions=
-o smtpd_sender_restrictions=
-o smtpd_recipient_restrictions=permit_mynetworks,reject
-o mynetworks=127.0.0.0/8
-o strict_rfc821_envelopes=yes
-o smtpd_error_sleep_time=0
-o smtpd_soft_error_limit=1001
-o smtpd_hard_error_limit=1000
再起動します。
[root@www ~]# systemctl restart postfix
Vsftpd をインストールします。
[root@www ~]# dnf -y install vsftpd
Vsftpd を設定します。
[root@www ~]# vi /etc/vsftpd/vsftpd.conf
12行目:匿名ログインを禁止します。
anonymous_enable= NO
83,84行目:行頭の「#」を削除してコメント解除し、アスキーモードでの転送を許可します。
ascii_upload_enable=YES ascii_download_enable=YES
101,102行目:行頭の「#」を削除してコメント解除し、chrootを有効にします。
chroot_local_user=YES chroot_list_enable=YES
104行目:行頭の「#」を削除しコメント解除し、リストファイルを指定します。
chroot_list_file=/etc/vsftpd/chroot_list
110行目:行頭の「#」を削除しコメント解除し、ディレクトリ転送を有効にします。
ls_recurse_enable=YES
115行目:IPv4を有効に変更します。
listen=YES
124行目:IPv6を無効に変更します。
listen_ipv6=NO
ローカルタイム指定を最終行に追記します。
use_localtime=YES
上層への移動を許可するユーザーを追加します。
[root@www ~]# vi /etc/vsftpd/chroot_list
ユーザー名を追記します。
webmaster
「/var/www/html」の書き込みを許可します。
[root@www ~]# chmod 0777 /var/www/html
起動します。
[root@www ~]# systemctl start vsftpd
自動起動を設定します。
[root@www ~]# systemctl enable vsftpd
「FFFTP」をダウンロード・インストールし、起動します。

「接続」をクリックします。
「接続」をクリックします。
「新規ホスト」をクリックします。
「ホストの設定名」に分かりやすい名前を決めて入力します。
「ホスト名(192.168.1.3)」を入力します。
「ユーザー名(webmaster)」を入力します。
「パスワード」を入力します。
「OK」をクリックします。
MariaDB をインストールします。
[root@www ~]# dnf -y install mariadb-server
MariaDB を設定します。
[root@www ~]# vi /etc/my.cnf.d/mariadb-server.cnf
[mysqld]に追記します。
[mysqld] character-set-server=utf8
起動します。
[root@www ~]# systemctl start mariadb
自動起動設定します。
[root@www ~]# systemctl enable mariadb
初期設定します。
[root@www ~]# mysql_secure_installation
下記の表示後、「Enter」を押下します。
Enter current password for root (enter for none):
root パスワードを設定します。
Set root password? [Y/n] y New password: Re-enter new password:
「y」で応答します。
Remove anonymous users? [Y/n] y
「y」で応答します。
Disallow root login remotely? [Y/n] y
「y」で応答します。
Remove test database and access to it? [Y/n] y
「y」で応答します。
Reload privilege tables now? [Y/n] y
MariaDBにrootユーザーで接続します。
[root@www ~]# mysql -u root -p Enter password:
ユーザー情報一覧を表示します。
MariaDB [(none)]> select user,host,password from mysql.user; +------+-----------+-------------------------------------------+ | user | host | password | +------+-----------+-------------------------------------------+ | root | localhost | ***************************************** | | root | 127.0.0.1 | ***************************************** | | root | ::1 | ***************************************** | +------+-----------+-------------------------------------------+ 3 rows in set (0.00 sec)
データベース一覧を表示します。
MariaDB [(none)]> show databases; +--------------------+ | Database | +--------------------+ | information_schema | | mysql | | performance_schema | +--------------------+ 3 rows in set (0.00 sec)
終了します。
MariaDB [(none)]> exit
phpMyAdminをダウンロードし、解凍します。
[root@www ~]# dnf -y install phpMyAdmin php-mysqlnd php-mcrypt php-php-gettext
phpMyAdminを設定します。
[root@www ~]# vi /etc/httpd/conf.d/phpMyAdmin.conf
13行目:アクセス許可IPを追記します。
Require ip 127.0.0.1 192.168.1.1/24
19行目:アクセス許可IPを追記します。
Require ip 127.0.0.1 192.168.1.1/24
再起動します。
[root@www ~]# systemctl restart httpd
Webブラウザを起動し、「http://fedoraserver.jp/phpmyadmin/」にアクセスし、登録したユーザーで認証してログインします。(管理画面から MariaDB を操作することができます。)
httpd をインストールします。
[root@www ~]# dnf -y install httpd
ウェルカムページを削除します。
[root@www ~]# rm -f /etc/httpd/conf.d/welcome.conf
httpd を設定します。
[root@www ~]# vi /etc/httpd/conf/httpd.conf
98行目:行頭の「#」を削除してコメント解除し、サーバー名を指定します。
ServerName fedoraserver.jp:80
154行目:変更します。
AllowOverride All
167行目:ディレクトリ名のみでアクセスできるファイル名を追記します。
DirectoryIndex index.html index.cgi index.php index.rb index.py
319行目:コメントアウトして文字化け対応します。
#AddDefaultCharset UTF-8
ドキュメントルート所有者を編集ユーザー(webmaster)に変更します。
[root@www ~]# chown webmaster. /var/www/html/
ドキュメントルート所有者を確認します。
[root@www ~]# ll /var/www/ 合計 0 drwxr-xr-x 2 root root 6 4月 24 22:46 cgi-bin drwxr-xr-x 2 webmaster webmaster 6 4月 24 22:46 html
URLのwwwを設定します。
[root@www ~]# vi /etc/httpd/conf.d/virtualhost-00-fedoraserver.jp.conf
wwwなしに統一します。
<VirtualHost *:80>
ServerName fedoraserver.jp
DocumentRoot /var/www/html
RewriteEngine On
RewriteCond %{HTTP_HOST} ^www\.fedoraserver\.jp
RewriteRule ^(.*)$ http://fedoraserver.jp/$1 [R=301,L]
</VirtualHost>
起動します。
[root@www ~]# systemctl start httpd
自動起動設定します。
[root@www ~]# systemctl enable httpd
HTMLテストページを作成します。
[root@www ~]# vi /var/www/html/index.html <html> <body> <div style="width: 100%; font-size: 20px; font-weight: bold; text-align: center;"> Test Page </div> </body> </html>
Webブラウザを起動し、「http://fedoraserver.jp」にアクセスし、動作確認をします。
ルーターの設定で、TCP80番ポートを開放します。(設定方法はご自身の環境に合わせて調べてください。)
こちらのサイトで「ホスト名(fedoraserver.jp)」、「ポート番号(80)」の開放確認をします。
Perl をインストールします。
[root@www ~]# dnf -y install perl perl-CGI
「html」ディレクトリで CGI の実行を許可する設定します。
[root@www ~]# vi /etc/httpd/conf.d/html.conf
拡張子 cgi、pl、rb、py を CGI として設定します。
<Directory "/var/www/html">
Options +ExecCGI
AddHandler cgi-script .cgi .pl .rb .py
</Directory>
「/usr/local/bin/perl」で、Perlコマンドへアクセスできるようにします。
[root@www ~]# ln -s /usr/bin/perl /usr/local/bin/perl
Perlのパスを確認します。
[root@www ~]# whereis perl perl: /usr/bin/perl /usr/local/bin/perl /usr/share/man/man1/perl.1.gz
再起動します。
[root@www ~]# systemctl restart httpd
CGIテストページを作成します。
[root@www ~]# vi /var/www/html/index.cgi #!/usr/bin/perl print "Content-type: text/html\n\n"; print "<html>\n<body>\n"; print "<div style=\"width: 100%; font-size: 20px; font-weight: bold; text-align: center;\">\n"; print "CGI Test Page"; print "\n</div>\n"; print "</body>\n</html>\n";
パーミッションを設定します。
[root@www ~]# chmod 705 /var/www/html/index.cgi
Webブラウザを起動し、「http://fedoraserver.jp/index.cgi」にアクセスし、動作確認をします。
PHP をインストールします。
[root@www ~]# dnf -y install php php-mbstring php-pear
PHP を設定します。
[root@www ~]# vi /etc/php.ini
923行目:行頭の「;」を削除してコメント解除し、自身のタイムゾーンを追記します。
date.timezone = "Asia/Tokyo"
再起動します。
[root@www ~]# systemctl restart httpd
PHPテストページを作成します。
[root@www ~]# vi /var/www/html/index.php <html> <body> <div style="width: 100%; font-size: 20px; font-weight: bold; text-align: center;"> <?php print "PHP Test Page"; ?> </div> </body> </html>
Webブラウザを起動し、「http://fedoraserver.jp/index.php」にアクセスし、動作確認をします。
Ruby をインストールします。
[root@www ~]# dnf -y install ruby
再起動します。
[root@www ~]# systemctl restart httpd
Rubyテストページを作成します。
[root@www ~]# vi /var/www/html/index.rb #!/usr/bin/ruby print "Content-type: text/html\n\n"; print "<html>\n<body>\n"; print "<div style=\"width: 100%; font-size: 20px; font-weight: bold; text-align: center;\">\n"; print "Ruby Test Page"; print "\n</div>\n"; print "</body>\n</html>\n";
パーミッションを設定します。
[root@www ~]# chmod 705 /var/www/html/index.rb
Webブラウザを起動し、「http://fedoraserver.jp/index.rb」にアクセスし、動作確認をします。
CPANを起動します。
[root@www ~]# perl -MCPAN -e shell
「y」を入力して「Enter」キー押下します。
Would you like to configure as much as possible automatically? [yes] y
チェックを入れて「OK」をクリックするとインストールログが表示されます。
モジュールをインストールします。
[root@www ~]#
ImageMagickをインストールします。
[root@www ~]# dnf -y install ImageMagick
perl ImageMagickをインストールします。
[root@www ~]# dnf -y install ImageMagick-perl
Certbotをインストールします。
[root@www ~]# dnf -y install certbot
証明書を取得します。
ドキュメントルート:/var/www/html/
メールアドレス:webmaster@fedoraserver.jp
Webサーバー名:fedoraserver.jp
[root@www ~]# certbot certonly --webroot -w /var/www/html/ -m webmaster@fedoraserver.jp -d fedoraserver.jp --agree-tos
証明書自動更新を設定します。
[root@www ~]# vi /etc/cron.d/letsencrypt
下記を追記します。
00 16 * * 2 root /usr/bin/certbot renew --post-hook "service httpd restart"
SSLをインストールして、暗号化通信ができるように設定します。
[root@www ~]# dnf install mod_ssl
SSLを設定します。
[root@www ~]# vi /etc/httpd/conf.d/ssl.conf
59行目:行頭の「#」を削除してコメントを解除します。
DocumentRoot "/var/www/html"
75行目:行頭の「#」を削除してコメントを解除し、変更します。
SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2
101行目:取得した証明書を指定します。
SSLCertificateFile /etc/letsencrypt/live/fedoraserver.jp/cert.pem
109行目:取得した鍵ファイルを指定します。
SSLCertificateKeyFile /etc/letsencrypt/live/fedoraserver.jp/privkey.pem
118行目:行頭の「#」を削除してコメント解除し、取得した中間証明書を指定します。
SSLCertificateChainFile /etc/letsencrypt/live/fedoraserver.jp/chain.pem
再起動します。
[root@www ~]# systemctl restart httpd
Free Monitoring Test Toolsで「https://fedoraserver.jp」の作動確認をします。